Technology
Hardware, software, networking, and development

#2694: Borg vs Restic vs Kopia: Best Linux Server Backup Tool
Borg, Restic, and Kopia compared for whole-server incremental backups on Ubuntu Docker hosts.

#2679: Can a VPN Protect You from SS7 Phone Spying?
SS7 is the hidden backbone of global phone networks—and it's wide open to spies. Here's what a VPN does and doesn't fix.
#2671: How Your Phone Helps Strangers Find Lost Wallets
Your phone silently helps strangers find lost items. Here's how the cryptography and mesh networks actually work.
#2670: Portable Projectors: What Actually Matters
Brightness, screens, and software longevity — what to look for when buying a portable projector.

#2667: Lost Phone, Found Tension: Security vs. Returnability
Can you secure your Android without killing the chance a good Samaritan returns it? We break down the tradeoffs.

#2660: Where the World's Best Dry Cider Lives
From Normandy's keeved ciders to Asturian sidra that argues with you — a global tour of craft cider's real hotspots.

#2659: How to Make Mead: Ancient Honey Wine's Revival
Mead predates the wheel. Here's how to brew it at home — and why it's making a comeback.
#2658: Off-Broadway vs Broadway: Seat Counts & Show Economics
Off-Broadway isn't just smaller Broadway—it's a different legal, economic, and artistic universe defined by seat counts.

#2646: Smart Locks & Networks: What Actually Works
Z-Wave vs Zigbee vs Wi-Fi for smart locks. What's reliable enough to trust with your front door?

#2629: Frankincense to Attar: Ancient Perfume Oils Today
How a frankincense obsession led to discovering perfume oils — a 4,000-year-old tradition that's being rediscovered today.
#2626: Smart Curtains vs Smart Glass: Bedroom Lighting Automation
Smart glass vs smart curtains for circadian health — what works in a rental bedroom without owning the walls?
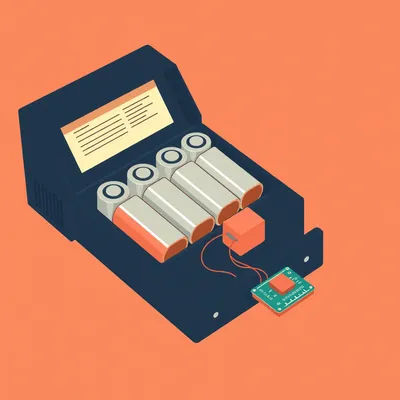
#2621: How 4 Batteries Produce 230 Volts
Four 18650 cells can't stack to 230V. The secret is switching, not stacking.

#2620: How Atomic Clocks Actually Keep Time
Why the second is defined by a cesium atom, not the Earth's rotation — and why leap seconds are causing chaos.

#2608: Building a House with KNX: Smart Home Infrastructure That Lasts
Can you wire your house like a hotel? Here's what KNX costs, how it works, and how to connect it to Home Assistant.

#2600: Circadian Lighting Gradients in Home Assistant
How to build a smooth, override-friendly circadian lighting system using Adaptive Lighting in Home Assistant.
#2599: Home 3D Printing in 2025: Keycaps, Cables & Real Costs
What $200 buys you for printing keycaps, cable housings, and small parts at home — with real material and environmental math.
#2597: Voice Control for Renters: $25 Per Room, No Wall Damage
Distributed voice control on a budget with wake words, centralized processing, and zero wall damage — perfect for rentals.
#2596: Systems Integrators vs MSPs: The Hidden Tech Career
Two parallel tech worlds: industrial systems integrators and IT managed service providers. How they differ, and why one pays $300/hour.

#2595: Baby-Proofing a Small Rental: Survival Strategies
Practical strategies for surviving the mobile baby phase in a small Jerusalem apartment without losing your security deposit.
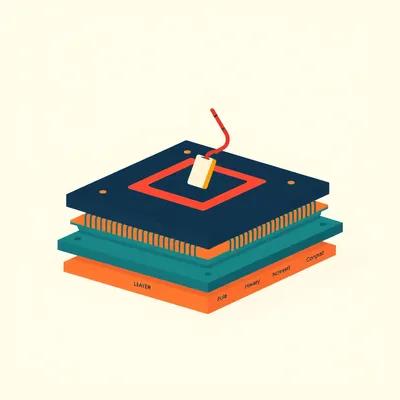
#2594: The Hierarchy of Immutable Code
From mask ROM to e-fuses: how hardware enforces a hierarchy of mutability in every computing device.